Last year, I was obsessed with the book, The Obstacle is the Way, The Timeless Art of Turning Trials into Triumph by Ryan Holiday. In the book, the author takes us back in time to visit with the writings of the Roman Emperor Marcus Aurelius, a general who recorded (for our benefit) how he met challenges in his diary, Meditations. And what we find time and time again is that whenever he was confronted by a new challenge or foe, he learned not to look at the immediate problem but rather how that problem could become the opportunity he was craving to make a leap forward in not only solving the immediate problem but, more importantly, fixing larger issues that were looming below the surface.
Fast forward to 2020 and we all are confronted with the security threats that we have to overcome. One issue that Security teams are challenged by is how to secure the modern remote workforce made up of contractors, developers, and remote workers who often bring their own devices (BYOD) and have a changing security posture as they travel the world throughout their workday. The obstacle of how to secure all of these workers is tough. But if we look to Marcus Aurelius, the actions of remote workers actually can become the way to a more secure enterprise.
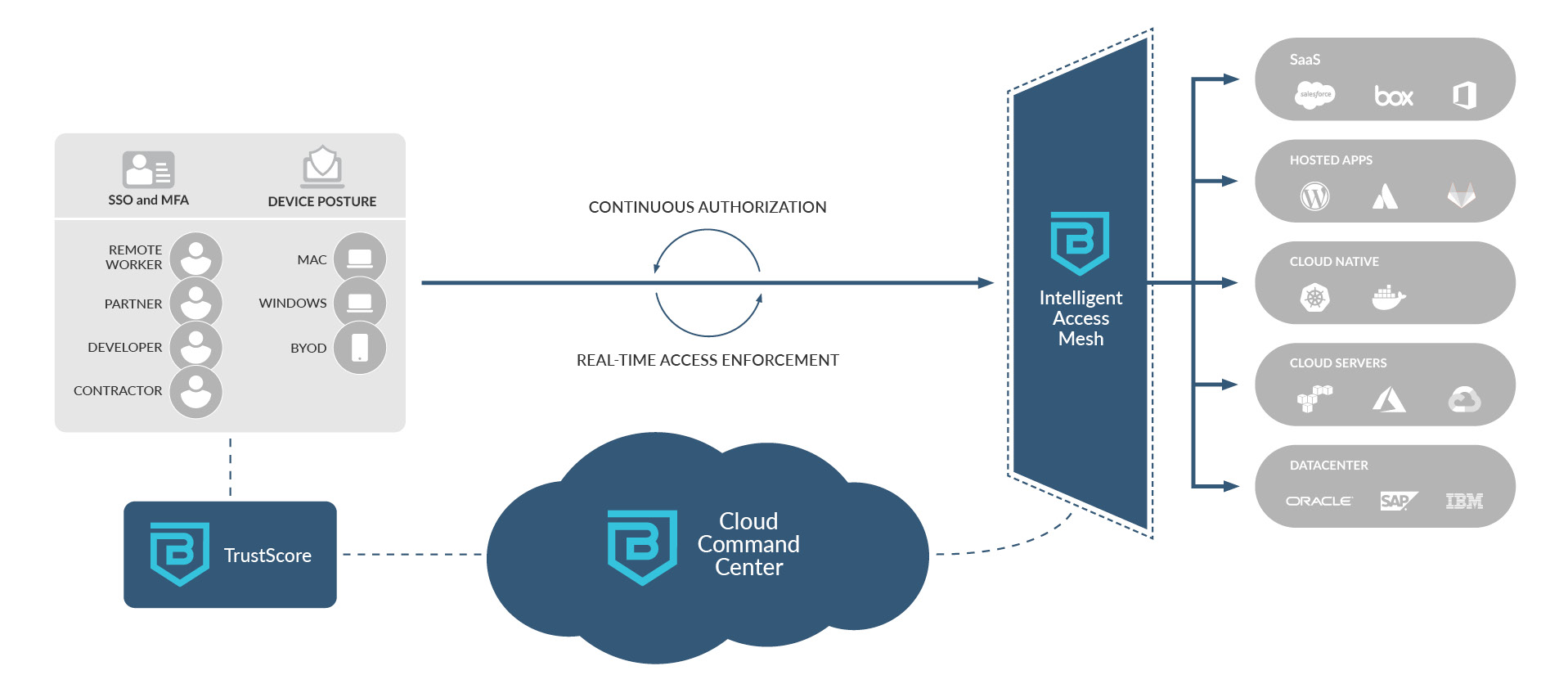
Here at Banyan Security, we believe that the answer lies in the same place as the perceived problem: the workforce. Those workers (contractors, developers, employees) who are trying to do their jobs but are constantly accessing valuable corporate resources used to be the source of the security problems. But with the way Banyan addresses Least Privileged Access and contextualizes each interaction and enforces control in real-time at the application layer, customers become more secure with each keystroke.
How Can Employees Help Improve Security?
Banyan has uniquely developed a TrustScore that encourages adherence to security policies. The TrustScore is something that is visible to each worker – on their devices as an application. The Security Team sets the threshold for the score, which will determine the level of access. This system sets this standard from 0-100 with 100 being the optimal score. Think of it in terms of a credit score. When your credit score is good, you have access to some basic level of credit. But when it is best, you get top-tier access to the best lending programs. Similarly, a worker with a score of 50 may only have access to the cafeteria app, but would not have access to a sensitive application like Salesforce. Our TrustScore application will not only inform the worker of their score but will also provide the remediation steps in order to get their score back to an acceptable range.

Some of our customers have taken this insight to new levels and have introduced gamification between teams and regions. They are posting the individual TrustScores and are actively tracking the teams that are succeeding as a group. Other customers use Banyan to help get the entire company to comply with a necessary security patch, for example. TrustScores are lowered across the organization with a single policy and quickly raised on each individual as soon as people have complied with the request.
With the Banyan solution, employees are empowered to be part of the solution. Traditional security tools have created a lot of barriers to access that have made workers less productive. It is hard to come up with creative credentials that are not repeated, and when they are forced to log in multiple times each day, people fall into patterns of repetition to speed things up. This ultimately leads to a less secure infrastructure.
Traditional VPNs Place an Undue Trust on Networks – Real-time Enforcement of Policies is Key
With the current state of VPN usage across the enterprise today, corporate assets are more vulnerable than ever before. Trusting the most critical assets of your enterprise to VPNs which, once breached, cannot stop an identity from lateral movement is dangerous.
Banyan’s Zero Trust solution provides a Distributed Access Tier, designed from the ground-up for today’s hybrid- and multi-cloud environments. At its core, the Access Tier is comprised of lightweight identity-aware proxies that use application-layer security mechanisms – Mutual-auth TLS (Layer-6) and OpenID Connect JWT (Layer-7) – to deliver transparent, secure network access.
A key advantage of operating at L6 and L7 is that the Access Tier can be deployed as pure software in a “service mesh” architecture. The mesh architecture allows us to enforce security policies close to your applications – wherever they run, be it on-premises, IaaS, or SaaS – which is required in a world where you no longer have a “trusted” corporate network.
Banyan is obsessed with user experience.
The only way this works is when the users are not impacted. With Banyan, users remain unaware of all the underlying, contextual analysis that is continuously authorizing every connection and request. Workers are only made aware that their TrustScore has changed, their access is limited and then they are provided with clear instructions about how to improve their security posture and get their score back to 100. Last year, we added Passwordless to the mix which has again made the user experience even more seamless.
Here at Banyan, we have seen that the Obstacle of secure access is also the Way to help make an organization more secure.
Meet with us to learn more about how to bring secure remote access to your team and organization. To schedule a demo, click here.
TL;DR
- The obstacle of securing the remote workforce is also the way to help make an organization more secure.
- Security teams are challenged in securing the remote workforce including employees, contractors, developers, and BYOD.
- Banyan TrustScores empower remote employees to help improve security by providing specific remediation steps to improve their scores, which results in overall better security.
- Traditional VPNs put corporate assets at risk. A breached VPN cannot stop an identity from lateral movement across the entire network.
- Banyan’s Zero Trust solution provides a distributed access tier to deliver transparent, secure network access that doesn’t affect the user experience.



