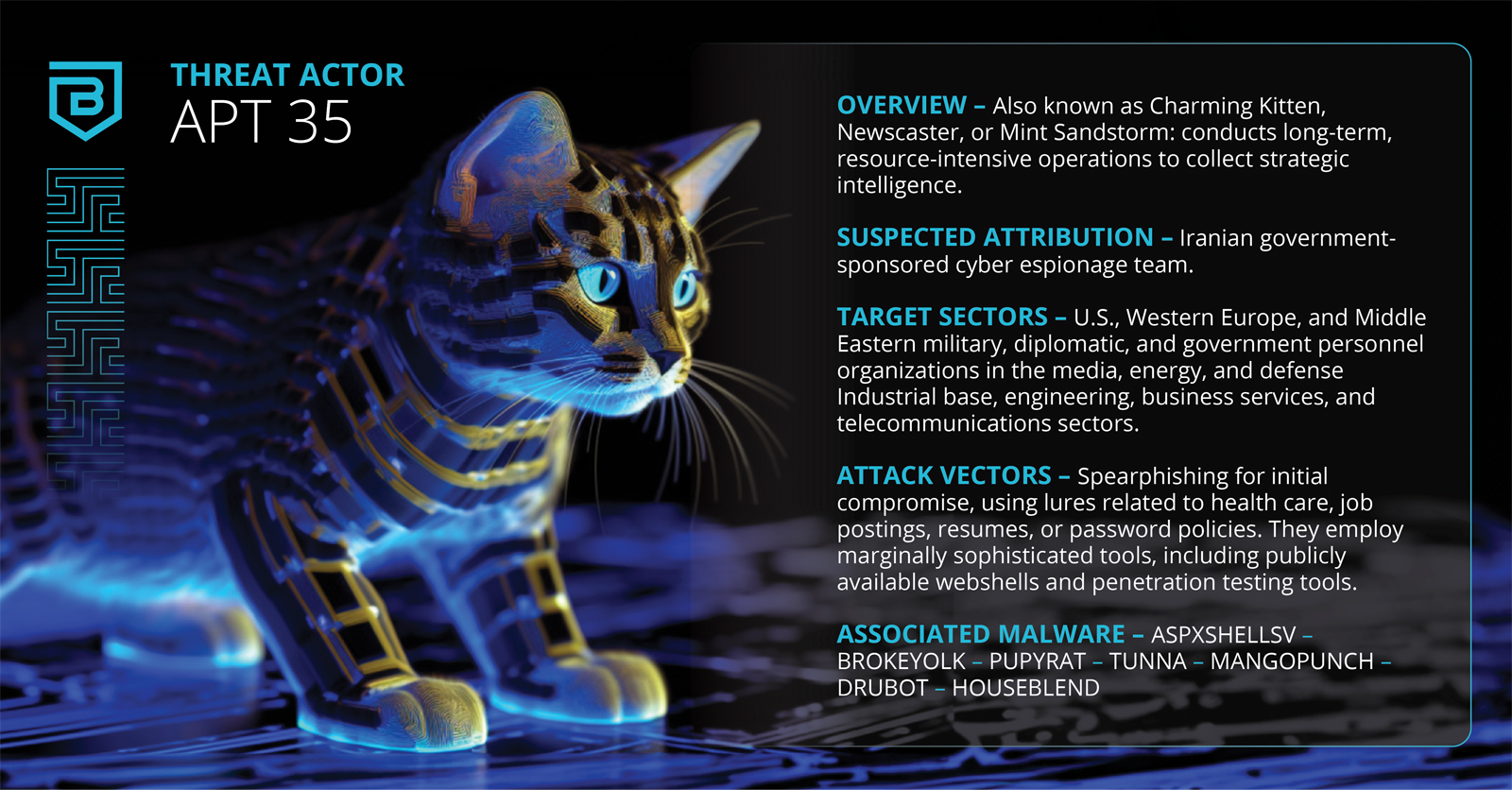
Overview: APT35, also known as Charming Kitten, Newscaster, or Mint Sandstorm, conducts long-term, resource-intensive operations to collect strategic intelligence.
Suspected Attribution: Iranian government-sponsored cyber espionage team
Target Sectors: U.S., Western Europe, and Middle Eastern military, diplomatic, and government personnel organizations in the media, energy, and defense Industrial base, engineering, business services, and telecommunications sectors.
Attack Vectors: APT35 typically relies on spearphishing to initially compromise an organization, often using lures related to health care, job postings, resumes, or password policies. They employ marginally sophisticated tools, including publicly available webshells and penetration testing tools. However, the breadth and scope of APT35’s operations indicates that the group is well resourced in other areas.
Associated Malware: ASPXSHELLSV, BROKEYOLK, PUPYRAT, TUNNA, MANGOPUNCH, DRUBOT, HOUSEBLEND