Transform Enterprise Security
Banyan provides granular zero trust policy controls and dynamic threat prevention.

Device Trust is the Foundation of Zero Trust
Upgrade MFA and eliminate credential loss and theft risks.
Device identity binds users to devices with cryptography, providing invisible MFA
Device posture reduces risk of malware spread
Clientless device trust via API integration with UEM/EDR for easy deployment

Security Service Edge (SSE) Prevents Threats
![]()
Block malicious web sites
& phishing attacks
![]()
Enforce zero trust policies
to internet access
![]()
Eliminate legacy bottlenecks
that reduce productivity
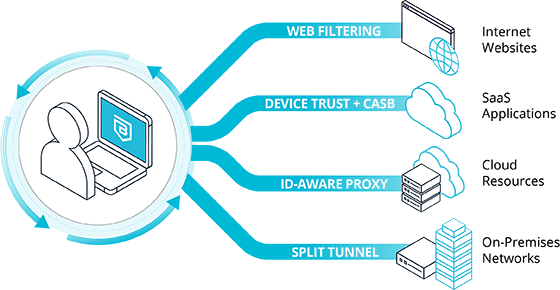
Lift and Shift SSE
Full tunnel | Always-on packet inspection |
Poor performance & UX
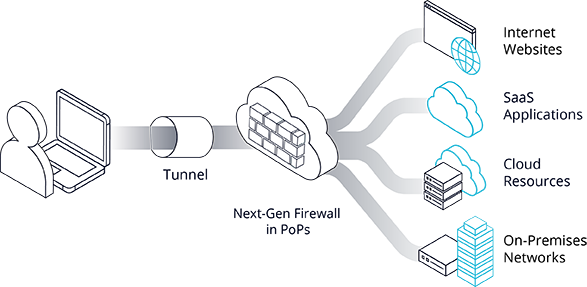
Banyan SSE
Intelligent routing | Always on, not always inline |
Great performance & UX

Comprehensive Visibility
Correlated user, device, security posture, and app activity
Inclusive visibility regardless of user or resource location
Easy to interpret dashboards, human-readable policy
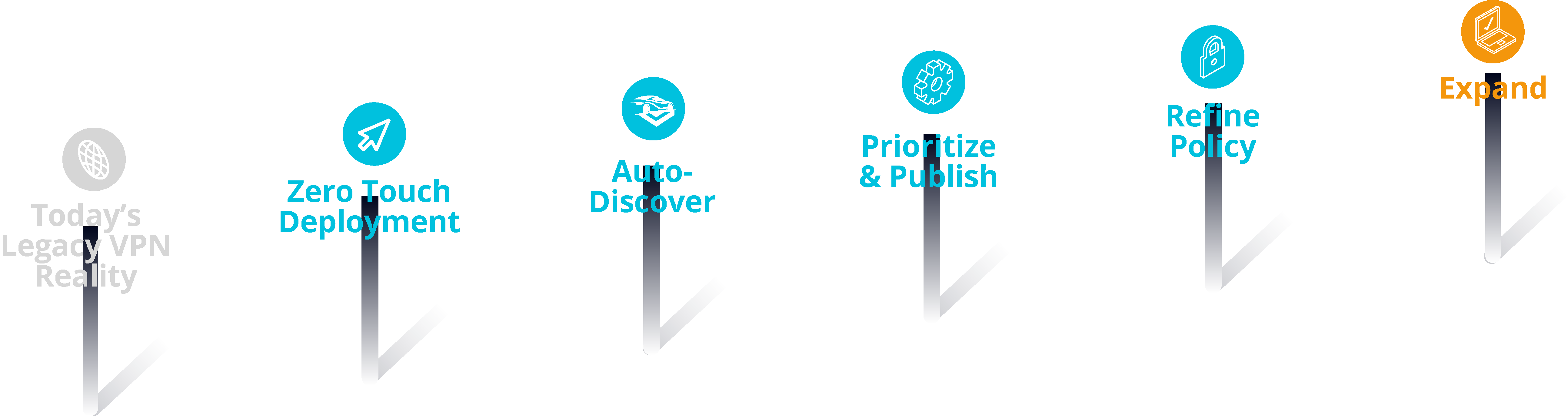
Lead the Journey to Zero Trust
Take the risk out of getting started, no “rip-and-replace” required
Deploy incrementally, reducing reliance on network-centric tools like legacy VPNs
Tie each deployment round to specific business outcomes
Zero Trust Achievements
User Trust | Device Trust | Least Privilege Access | Continuous Authorization

Integration with Security Stack
Leverage MDM/UEM for zero-touch installs
Use Endpoint Detection and Response (EDR) device telemetry data in trust scoring
Banyan APIs permit both automation and data access for use in downstream solutions like SIEM
