Zero Trust Network
Access (ZTNA)
Comprehensive, secure access to on-prem, hybrid, and multi-cloud infrastructure and applications – from anywhere.
Why You Need ZTNA
Traditional network-centric access solutions like VPNs present serious limitations and challenges for enterprise customers, including high costs, complex management, scalability issues, and security risks. Organizations are increasingly taking advantage of Zero Trust Network Access (ZTNA) to enable employees and third parties to access on-premises, hybrid, and multi-cloud applications and infrastructure from anywhere.
Banyan Security’s ZTNA offering works consistently, regardless of worker location, enabling least-privilege access to hosted applications and infrastructure based on real-time contextual factors including user and device trust scoring and resource sensitivity. Best of all, it is easily managed and provides a great user experience.
Banyan Zero Trust Network Access
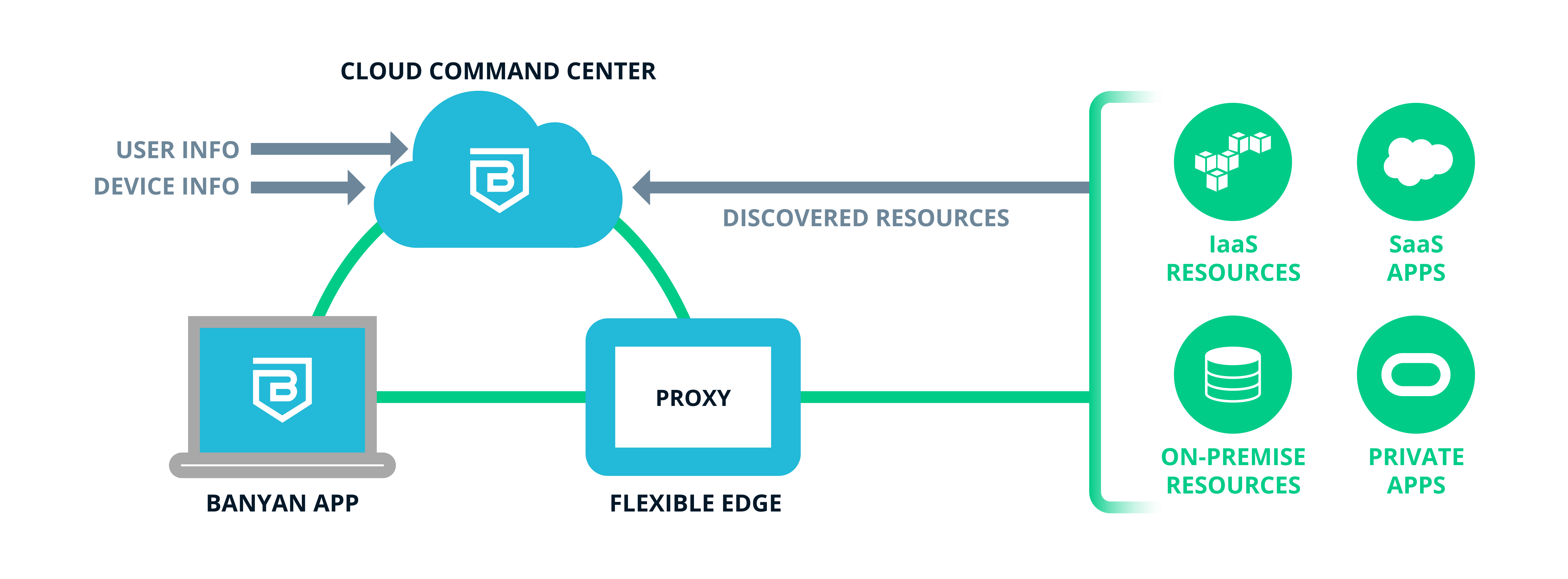
Banyan ZTNA consists of three main components:

Cloud Command Center
A trust level is calculated based on the user ID, device ID, and device security posture then evaluated against policy, and if approved, short-lived certs are issued to permit access, which is now a direct path to the approved application or resource.

Flexible Edge
Access requests are received by the Flexible Edge, then fully vetted by the Cloud Command Center (which is tied into your IdP as well as your existing Endpoint Detection & Response (EDR) and Unified Endpoint Management (UEM), if desired).

Banyan App
Since Banyan employs continuous authorization, should the user’s trust score drop to an unacceptable level, existing access sessions are suspended. They can go to the Banyan app, see what adversely affected their Trust Level and self-remediate.
How Banyan ZTNA Works
Banyan ZTNA Advantages
Banyan ZTNA is the best choice for cloud-forward organizations providing the modern workforce easy, secure access to on-premises, hybrid, and multi-cloud applications and infrastructure from anywhere. Our solution offers numerous advantages over legacy products, including:
Easy to deploy, manage, and use.
- Cloud-managed centralized configuration platform (Cloud Command Center).
- Banyan’s Flexible Edge deployment model can be deployed in seconds locally next to the resource (we call this “Private Edge”), or with a lightweight Connector that interfaces with cloud-based PoPs (the “Global Edge”).
- Runs alongside existing VPN if desired, allowing low-risk incremental deployment by application or user group, retaining safety net of existing legacy services.
- Banyan works seamlessly with IaaS and PaaS environments providing one-click access to corporate applications as well as resources like SSH/RDP servers, Kubernetes, and databases. Least privilege access allows differentiated access for employees and third parties alike that is a snap to deploy, administer, and audit.
- Seamlessly integrates with existing Identity Provider (IdP), Endpoint Detection and Response (EDR), and Unified Endpoint Management (UEM) investments, not to mention automation integration with DevOps tooling (think “Zero Trust as code”).
- Consistent, simple user experience that is always the same no matter where they happen to be.
Unmatched security.
- Least-privilege access ensures workers only have access to the resources they need to do their jobs.
- Fine-grained controls use Banyan’s trust score-powered policy engine, enabling continuous authorization based on user and device trust, device security posture, and resource sensitivity. Banyan aligns the risk of the request with the sensitivity of the resource, revoking access mid-session if warranted.
- A single policy governs users, whether on-campus or remote, removing risk of coverage gaps.
Visibility drives action.
- Interactive dashboards show zero trust achievement.
- Deep visibility into user, device, app, and service activity, permitting superior control and accountability. And, automatic Discover & Publish capabilities make it a snap to know what’s available to be published.
Discover More about Banyan ZTNA
Solution briefs and videos to get you started.
Get the Data
Use our Banyan ZTNA datasheet to see an overview of implementation steps and considerations.

Migrating to ZTNA
Get the quick overview on how simple migrating to Banyan ZTNA can be with Ashur Kanoon.
