Quickly Deploy and Use
Tired of constantly onboarding and offboarding people and dealing with password changes? Let’s put an end to it now. Quickly deploy a modern, cloud-based VPN (VPNaaS) with zero trust benefits using the Banyan Security Platform Team Edition. Easily deployed without complex integrations, this secure solution is easy to manage and easy to use.
- Deploy in minutes
- No credit card required
- Easily create bundles of related services making for easy, one-click access
- Least privilege access allows differentiated access for FTEs and third parties alike that is a snap to deploy, administer, and audit
- Sleep easy with zero trust continuous authorization based on real-time user, device, and application context

Why Suffer?
Networking, Security, and DevOps folks have been putting up with poor application and infrastructure access solutions for years. Banyan puts an end to this nonsense.
- Save time by eliminating legacy VPNs, bastion hosts, inbound firewall ports, or PKI/cert management
- No more inconsistent, unpredictable performance
- No juggling easily lost/compromised credentials for each chunk of infrastructure
- No more insecure, inconsistent user experiences

Easy Installation
Once signed up, installing Banyan in your own environment couldn’t be easier – it’s just a few simple steps:
1. Install Connector
The Banyan Security Connector installs next to the service or app you wish to access.
2. Download Banyan App
Download the lightweight Banyan app and complete registration.
3. Define Access Trust
Create a new service and define the access trust level requirements.
4. Invite Users
Invite users to download the Banyan app and register their devices.
Be a Zero Trust Hero!
Why make users juggle separate access credentials for every chunk of infrastructure they need to do their job? Banyan Security makes easy, one-click access a reality that users will thank you for.
![]() Service Catalog features Service Bundles, Favorites, and Autorun capabilities for seamless access
Service Catalog features Service Bundles, Favorites, and Autorun capabilities for seamless access
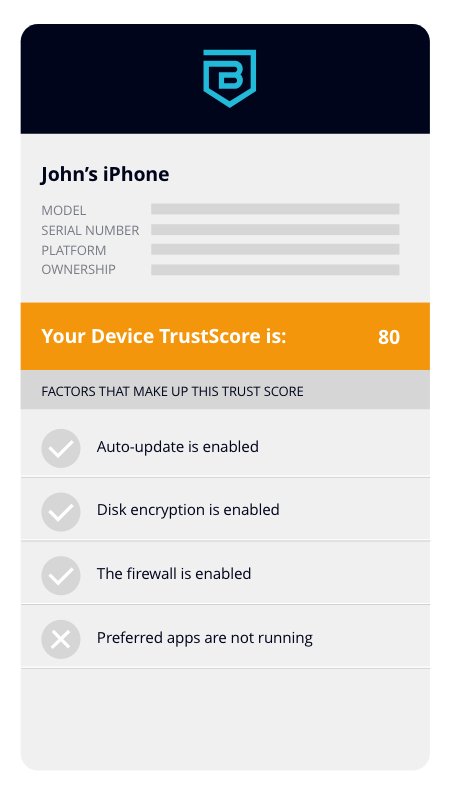
![]() Users see their device’s security posture and are able to remediate without IT or Security assistance
Users see their device’s security posture and are able to remediate without IT or Security assistance