 It’s popular because it’s profitable and it’s been a big moment for ransomware around the planet over the past few weeks. At Banyan, we decided to assemble the latest ransomware news for a mid-May Ransomware Threat Update (because there’s been enough of it to warrant its own blog). Ransomware has become ever more targeted, with its strategists becoming more and more creative, especially as the average ransomware payout declined almost 40% last year. A new trend we’re seeing is around double- and triple- extortion, where employees are threatened with the release of personal sensitive data (selfies…medical records…) along with corporate data. As a result, ransomware negotiations have gotten much more nuanced for all involved.
It’s popular because it’s profitable and it’s been a big moment for ransomware around the planet over the past few weeks. At Banyan, we decided to assemble the latest ransomware news for a mid-May Ransomware Threat Update (because there’s been enough of it to warrant its own blog). Ransomware has become ever more targeted, with its strategists becoming more and more creative, especially as the average ransomware payout declined almost 40% last year. A new trend we’re seeing is around double- and triple- extortion, where employees are threatened with the release of personal sensitive data (selfies…medical records…) along with corporate data. As a result, ransomware negotiations have gotten much more nuanced for all involved.
Ransomware Threats Take a Hit – DOJ Charges Wazawaka
Mateev on the run: In other big ransomware news, the U.S. DOJ unsealed indictments Tuesday, May 16 accusing Mikhail Pavlovich Matveev aka “Wazawaka,” a Russian national, of the following: conspiring to transmit ransom demands, conspiring to damage protected computers, and intentionally damaging protected computers. Since 2020, Matveev allegedly collaborated from Russia with other hackers using ransomware variants including LockBit, Hive and Babuk. His activities are linked to $200 million in ransom from around global 2,800 victims, which included hospitals, businesses, nonprofits – including churches and charities – and government agencies. He’s still on the loose, though, and a $10 million USD reward might not be enough to find him (which is a really big bug bounty). He’s known for trolling Brian Krebs earlier this year and also is missing a finger, so keep your eyes open.
Educators, beware: CISA and other agencies have warned of attacks carried out against Education targets by a threat actor known as the Bl00dy Ransomware Gang, who began striking in early May. Bl00dy gained access to victim networks across the Education Facilities Subsector, where PaperCut servers vulnerable to CVE-2023-27350 were exposed to the internet. Note: in an attempt to mask malicious traffic and avoid detection, the Bl00dy actors use TOR and other proxies from within victim networks for external comms.
Ransomware Threats Everywhere – New Kids on the Block
Getting the Royal treatment – “Most likely what happened is you decided to save money on your security…” is how Royal started its ransomware note to the city of Dallas. Some websites–like those for municipal courts and libraries–are still down three weeks after the initial attack on the city of Dallas, Texas. Made up of former members of the Conti cybercrime syndicate, the Royal ransomware group is thought to be behind the attack. If you’re in healthcare, pay attention: Royal has been involved in high-profile attacks against critical infrastructure (especially healthcare) since first emerging in September 2022. 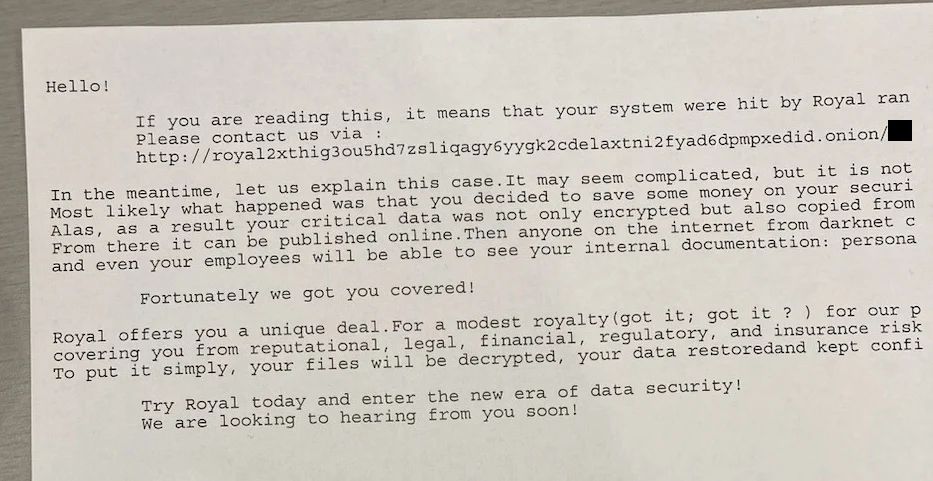
New Actor – RA Group: Cybersecurity researchers from Talos have uncovered a threat actor called RA Group, which first kicked off its operations in late April using previously leaked Babuk source code. It launches double-extortion attacks, stealing sensitive victim personal data as it encrypts systems (to motivate the victims to pay the ransom demand out of fear of personal compromise). When RA Group leaks the data, it discloses the name of the victim, a list of the stolen data, the total size, and the victim’s website, just to be extra-thorough…
MalasLocker and Zimbra: Also heating up this May, more reports of MalasLocker ransomware, which targets Zimbra servers to steal email and encrypt files, and finally finishing with a demand for a ‘charity’ donation. Instead of demanding a ransom payment, the threat actors instead request a donation to charity before they provide an encryptor and stop leaking data. The operation began encrypting Zimbra servers towards the end of March 2023, with victims reporting in both the BleepingComputer and Zimbra forums that their emails were encrypted.
–
Curious how Banyan can help prevent ransomware? Schedule a custom demo today.
*Researched and authored by Mademoiselle



