Solving remote access productivity and security challenges for software engineering teams
Today, DevOps has a hard time providing easy, fast, and secure remote access to developer resources in hybrid and multi-cloud environments. In a post-COVID world, where work-from-anywhere and cloud is the norm rather than the exception, it’s crucial to provide quick access while ensuring productivity and security. Developers are adversely affected by the multiple logins required across heterogeneous environments, the risk created by the VPN’s over-privileged access grants and lack of device trust.
Challenging Day(s)-in-the-Life of DevOps
In talking with Banyan Security customers, we uncovered many challenges faced by DevOps teams. Let’s talk about Mike and his DevOps team who manage critical infrastructure including VMs, Kubernetes clusters, and databases as well as development resources like Jenkins and GitLab. They support different environments like dev, staging, pre-prod, and prod in their private data center or IaaS (e.g., AWS).
To access services, they use a traditional VPN in order to connect to the bastion host(s) which in turn allows them to gain access to their infrastructure. For each hop, their IT team needs to configure inbound firewall ports and manage siloed authentication systems for each service such as web, SSH, and databases.
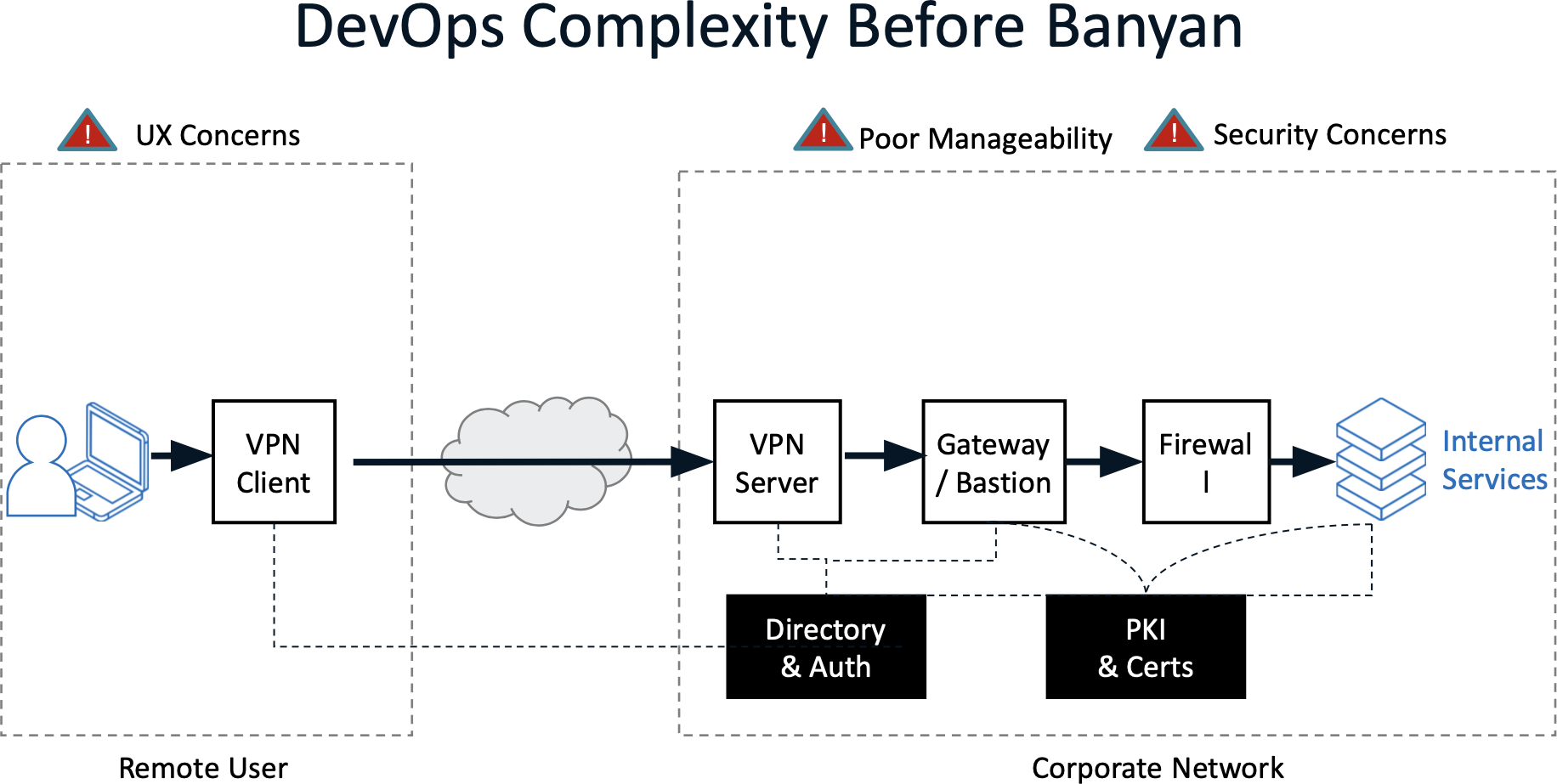
There are three main problems with this approach:
- Manageability – Teams need to configure and maintain IP whitelisting rules in their VPN, rely on static SSH keys in bastion host(s), coordinate firewall rules with different teams, and document application-specific authentication. The coordination and execution of so many touch points for common actions including the onboarding of new team members, changing roles, or adding a new service invite mistakes that cause productivity issues and introduce unforeseen security holes.Every week, Mike’s team needs to on-board new employees, remove access from previous employees, and add/remove services. In this example, Mike has hired a new developer, Alice. He wants to give her a great user experience and make sure she can hit the ground running on day one with easy, fast access to hosted developer tools and staging environments. He wants to provision and automate access without needing to touch multiple systems or file multiple support tickets. Last but certainly not least, Mike wants to ensure each user and device connecting to their infrastructure adopts a zero trust approach following a principle of least privilege. For example, Alice needs access to development environments, but shouldn’t have access to production systems.For each employee or service to be added/removed, it takes 4 tasks across 4 different teams with each task having 4 actions (new ticket, provision/de-provision access, end-user setup and typically some troubleshooting). This typically takes days to weeks.
- User Experience – Developers have to go through multiple steps to get access to services they need. Get onto VPN. Get through bastion. Authenticate with the service. Even worse, they often have no idea what corporate resources they have/need access to for different projects and these authentication systems.
- Security – VPNs and bastions grant broad network access. In many cases there is no centralized audit log. Static credentials lead to an increased risk of leakage.
Better way with Banyan!
If you can relate to Mike’s challenges, Banyan Security has delivered a better way!
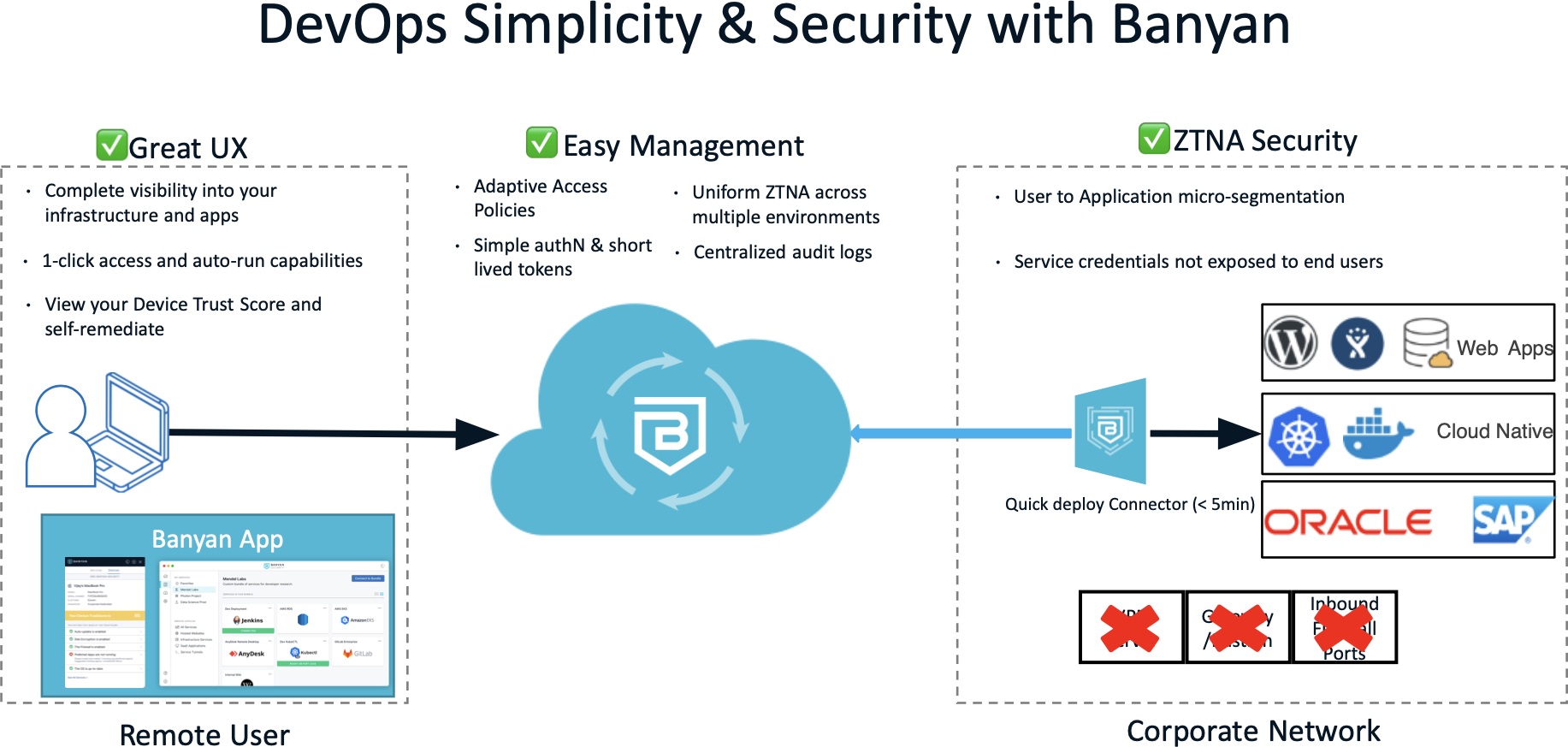
-
- Manageability – Mike simply deploys a Banyan Connector in his infrastructure network in a few minutes (no outbound firewall ports or DNS entries to worry about) and defines Services in the Banyan Command Center. When Alice joins, all that has to happen is to add her into the right group(s). Once employees are provisioned or de-provisioned by the Identity Team, they get access to the services they are entitled to. If it’s a new service, all Mike’s team needs to do is add the new service in the Banyan Command Center and assign it to the right groups.
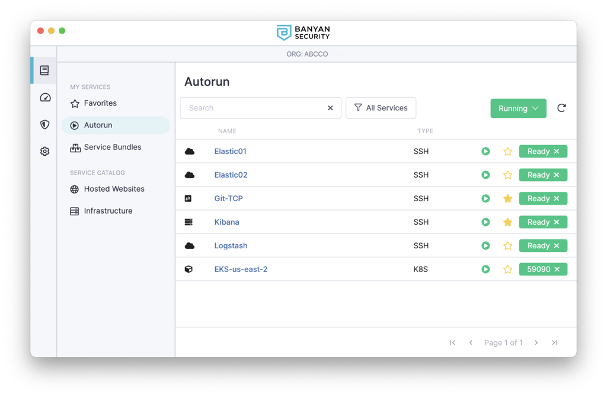
- User Experience – When Alice logs in via the Banyan app, she sees a well-categorized Service Catalog showing all of the services she needs to do her job. A single ‘click’ on a particular service gets her connected, but if she so chooses, there’s a CLI available for her use. Services can also be tagged to auto-run so Alice can get one-click access to those services.
- Security – Alice has been granted access to the specific services she needs to be productive rather than overly-broad access to entire network segments. The Command Center provides admins detailed audit logs of what they’re accessing. Revoking access is as easy as removing them from a group, or adjusting a policy. Over time, Mike can also apply Trust-Based Access Controls where granular policies ensure access is predicated on appropriate device trust score thresholds being met. Rather than a single check prior to granting access, these production services policies continuously assess the security of the users and devices accessing the services.
Banyan Security is committed to enabling productive and secure remote access for software organizations! Teams get easy, simple access to infrastructure services and hosted applications through one-click access, enhanced visibility into how services are accessed, and protect their services with rock solid security built on zero trust access. To democratize zero trust access for all kinds of organizations, we are making all of this available to you at NO charge with Banyan Security Team Edition. So go ahead, download for free and start getting the best zero trust remote access. Drop us a note – we’d love to hear your feedback!
Get Team Edition here: https://net.banyanops.com/create-banyan-account/



