This is the first in a series of blogs on “How To Zero Trust”, geared towards enterprise IT and security professionals. Our objective is to highlight real-world scenarios and practical solutions to improve the security posture of your organization toward Zero Trust access control. In this first post, we’ll address a common question we hear from many enterprise security professionals: How should an enterprise extend its Cloud Single Sign-On (SSO) to get to move toward a Zero Trust security posture?

Consider this scenario – your organization is rapidly migrating apps to the cloud to cut costs and improve business agility, and has invested in a cloud-based identity provider such as Okta or AzureAD. However, your employees are still stuck using their traditional VPN. You realize it is time to move past an on-premises VPN-based security model to a modern cloud-integrated Zero Trust model, and you can clearly see how a framework like Google’s BeyondCorp could benefit your organization, but it all just seems overly complicated and intimidating. Device inventory, trust inference, authorization policies, certificate management, access control engine… where does one even start? Who will manage all this? Is it even worth it? To make matters worse, your teams just don’t have enough time or resources. So, just how do you roll out Zero Trust?
The Essence of Zero Trust
Let’s start by boiling down Zero Trust to its essence: a Zero Trust security model is one that does away with the idea of a privileged network. Instead, access depends solely on device and user credentials, regardless of network location or application hosting model. This means all access to enterprise resources must be fully authenticated, authorized, and encrypted based upon device state and user credentials.
Thus, instead of relying on your network perimeter to safeguard your enterprise, with Zero Trust you rely on:
- Securely Validating the User – Have appropriate information about all users that need to access enterprise resources; validate primary and second factor credentials for users requesting access to our enterprise resources.
- Securely Validating the Device – Collect sufficient knowledge of all devices that need to access enterprise resources; validate device posture in real-time and keep track of changes as a device progresses through its life cycle.
- Policy-based Access to Applications – Apply the “Principle of Least Privilege” so access to corporate resources is only permitted to employees who need it to do their job.
And, that’s all there is to it!
SSO is the First Step
As you can see, your investment in a cloud-based identity provider and migration to cloud-based SSO is a great starting point. Most SSO vendors also provide Multi-Factor Authentication (MFA), which you should enable where appropriate, so you can ensure secure user authentication via primary and second factor credentials. With your SSO strategy in place, you have checked off the first requirement for Zero Trust – securely identifying users accessing corporate resources.
From SSO to Device Trust
The next step towards Zero Trust is to create an inventory of all your devices. This is a crucial step because a Zero Trust model requires that network location be immaterial; instead, access to corporate applications is only granted to trusted devices.
If your organization has mature desktop and mobile device management (MDM) and private public key infrastructure (Private PKI) capabilities, this step is fairly straightforward as well. You can use your device management solution to deploy a device certificate to all your endpoints so you can uniquely identify the device and attest to its status. If your SSO vendor also offers device identification, you can enable it to enhance this process. In addition to simply identifying the device, it is important to validate the device posture, or how much risk this device is introducing into the request process. Anti-virus, MDM, EDR, SIEM and other such solutions can help with this validation, and they should be part of the Zero Trust integration to establish the overall trust of the request. This will help in the next step to determine what resources are safe to access from this device.
The device inventory step can get more complicated if your organization uses disparate device management tools, allows Bring Your Own Device (BYOD) programs or needs to manage access for multiple third-parties. In such cases, you’ll need to create a meta-inventory database to amalgamate and normalize device information from multiple sources, and enable a lightweight process for third-parties to register their devices. You should leverage your existing tooling where possible, instead of replacing or duplicating their capabilities.
From Device Trust to Zero Trust
Once you have the ability to securely identify your users and devices, you can focus on your applications. Enterprises today run their corporate applications and services across diverse environments – on-premises in datacenters, in cloud IaaS environments such as AWS and Azure, and in cloud SaaS environments such as Salesforce and Dropbox.
You should start by creating a general policy framework for your organization, that applies regardless of where an application is hosted. Start with a set of “Global Rules”, that are coarse-grained policies that affect all corporate resources. For example, you could create a classification system that creates tiers of applications based on the sensitivity of the data handled. Then, you could specify that applications in the “high-sensitivity” tier can only be accessed by users authenticated using SSO on trusted devices registered with your device manager. As you create Global rules, you can also start developing Service-level rules that apply to individual applications and typically involve assertions about the user, as well as resource-specific rules that take policies down to the API-level. If your organization is investing in DevOps and cloud-native development, be sure to include applications and services deployed in those environments – SSH servers, IaaS consoles, Kubernetes APIs, CI/CD tools, etc. – in your framework.
One of the core tenets of modern Zero Trust implementations is to avoid blanket network access technologies such as VPNs, VLANs, etc. Instead enforce access control policies using application-layer techniques, such as an Access Proxy, that provide the uniform coverage and granular controls needed for today’s enterprise environments. With the right enforcement mechanisms in place, you can now apply application controls to match your organization’s policy framework.
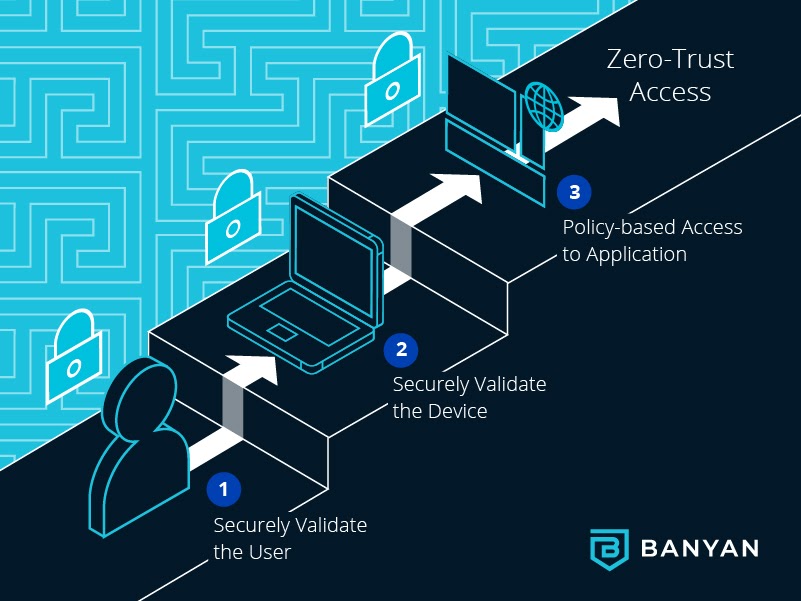
Securely Validate the User -> Securely Validate the Device -> Policy-based Access to Applications
As you can see, the conceptual pieces needed to implement Zero Trust/BeyondCorp security are straightforward. If your enterprise runs entirely on Google Cloud using Google products (such as, GSuite Enterprise, Google Identity SSO & MFA, Google Endpoint Management, Google Cloud Platform, etc.), then read no further. Simply hop over to Google’s BeyondCorp Remote Access offering, work through their checklist and you’ll have a Zero Trust posture rolled out in no time. For those of you who are not operating in a 100% Google environment, you will need to go beyond BeyondCorp – read on.
Implementing Zero Trust in the Real World
Now, if your organization does not run entirely on Google or have the engineering resources to dedicate to a homegrown Zero Trust project, Banyan can help. Once you have your SSO in place, Banyan can accelerate your Zero Trust journey.
For Device Trust, Banyan offers multiple deployment options that you can tailor to your organization’s needs. Banyan integrates with your Device Manager for secure device identification and other tools such as AV, EDR, SIEM, NAC, and others for posture validation on managed corporate devices. For BYOD, third-parties and other scenarios, Banyan also provides desktop and mobile apps that can perform device attestation and posture reporting. Exceptions can be granted to unknown devices in order to support incremental roll outs. In either case, Banyan supports continuous validation to reject access at any time, as necessary.

Banyan apps for all Devices
For policy-based access to applications, we provide an access proxy and policy engine that uses seamless integrations to enable click-button access controls across your diverse environments – on-premises, cloud IaaS, cloud SaaS – with comprehensive policy definition and enforcement.
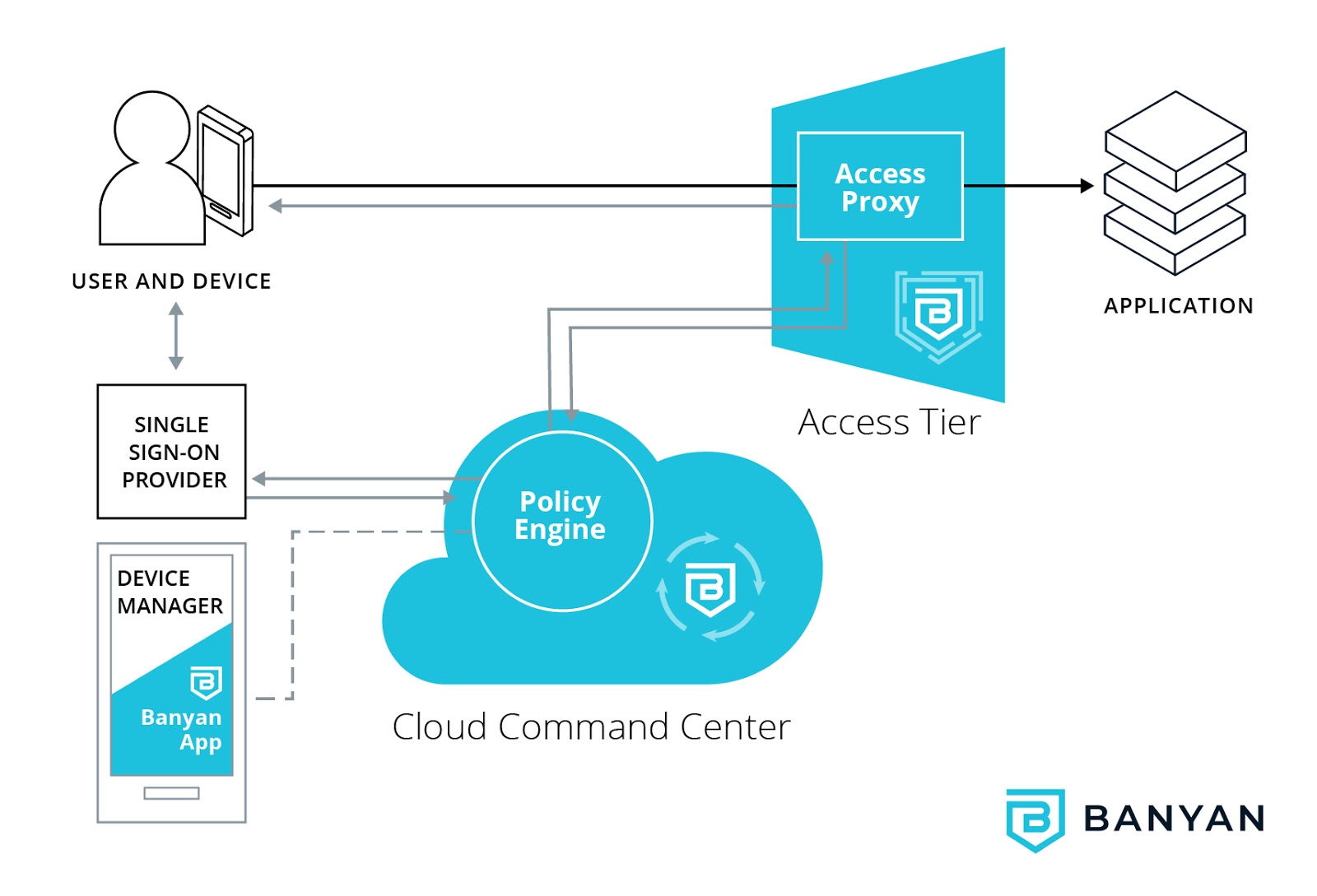
Banyan Zero Trust Authorization Flow
Banyan is designed to make it easy for your IT teams to roll out Zero Trust. And best of all, it is designed for incremental roll-out in complex environments. Decide the best approach for your unique scenario (such as tackling the toughest apps first, then configuring simple apps; establishing a few key users first, then departmental roll-outs, etc.).
In summary, once you have SSO in place, Banyan can help you configure the rest of your enterprise environment for a Zero Trust security posture. Get ready to Zero Trust!



